5 Emotions Used in Social Engineering
Beauceron Security
Are you being bombarded with phishing emails? Are you worried even the most basic phish can infiltrate your organization? In this blog, we explain how social engineering works, how cybercriminals target your emotions and how to spot a potential phish.
What is Social Engineering?
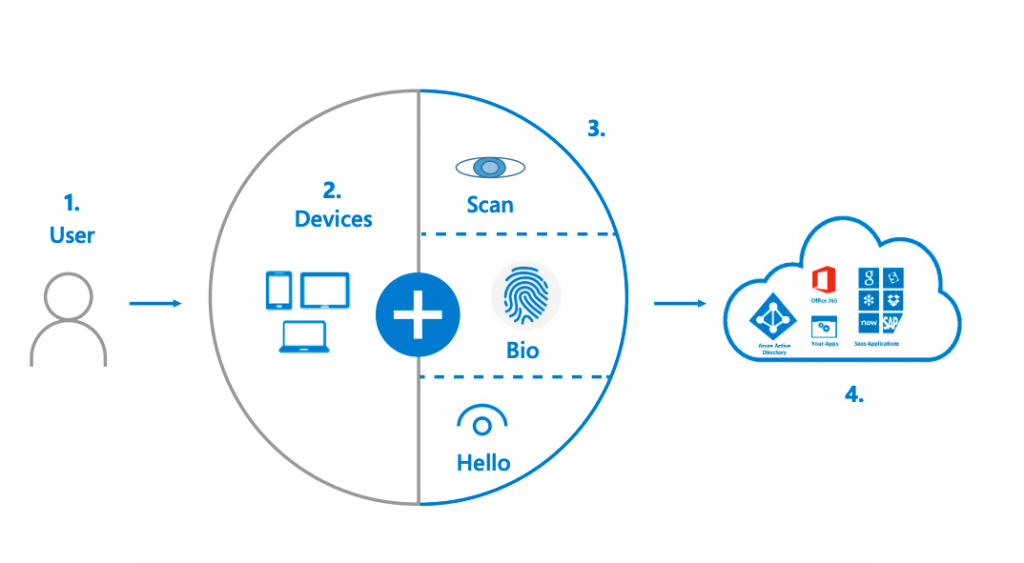
Social engineering is a highly effective way for cybercriminals to gain unauthorized access to your personal, private information through your phone, laptop or other electronic device. Cybercriminals craft scams which prey on your emotions in an attempt to have you act quickly without fully considering the situation.
What Emotions are Targeted in Social Engineering?
-
Fear
-
Greed
-
Surprise
-
Anger
-
Curiosity
Why Do We Fall for Phishes?
By exploiting emotions such as fear, greed, surprise, anger or curiosity, cybercriminals are looking for you to act on those emotions without thinking critically about the situation. Psychologist and economist, Daniel Kahneman, explains how this works through a model of two systems of thinking:
System 1 is fast and intuitive. This is the system that deals with emotional responses and decisions that we make on a daily basis. Every day we are faced with thousands of decisions: from which sock to put on first to how much cream we want in our coffee. If we had to deliberate and think critically about every little decision, we wouldn’t be able to get anything done. This is why we depend so heavily on System 1. System 1 relies on mental shortcuts, or “auto pilot” responses which help alleviate the mental burden of making all these decisions. However, System 1 can also harm our decision making. Kahneman states that all humans have a truth bias, or a belief that folks generally tell the truth rather than lie, a belief that can lead to clicking on a suspicious or unbelievable email attachment, for instance.
System 2 is deliberate and slow. This is the system that we use when making difficult decisions that require us to slow down and consider our options, like if we should change career paths or buy that new car. Cybercriminals depend on us not using this type of decision making and instead relying on our emotions and System 1 response.
What Tactics Do Social Engineers Use?
Authority: These types of attacks are popular with phishing and vishing. Most folks don’t want to get into any legal trouble, so they go along with the ploy. These attacks typically play on the emotion of fear, as people are afraid of getting in trouble with the law or another authority figure.

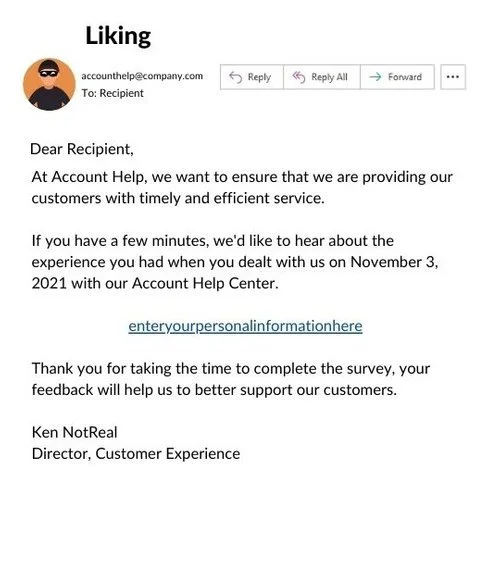
Liking: It’s a known fact that people like folks that are charming or helpful. This tactic could be used in vishing and phishing attacks and is sometimes mixed with Reciprocity. Generally, a cybercriminal will reach out pretending to be helpful and charming for you to give them personal information such as login credentials, SIN or other classified information. These attacks can prey on emotions such as curiosity and surprise.
Scarcity: Is a popular phishing technique that usually involves quantity or time constraints. For example, you may receive an email from a higher-up in your organization demanding that you click on a link to complete a task in 15 minutes or else! These types of attacks prey on emotions like fear or surprise as the email is unexpected and you most likely are afraid of the consequences of not completing the action demanded.

Social Proof: Consists of name dropping to trick folks into thinking you have the authority to make specific demands. For example, a cybercriminal could ask you for your login credentials by pretending to either be your boss or someone else who works for your company. This method of social engineering depends on the emotions of fear and surprise.

Reciprocity: Is when you are asked to provide information because you have been given something. For example, you could receive an email stating that you have been offered a raise if you click on the link provided and enter your personal information. This tactic depends on the emotions of surprise, curiosity and even greed.

How to Spot a Phish
Look Suspicious? – If you receive and email from an address that you don’t recognize or receive a request that is unusual – don’t do it! Always double check that this is a task that you have been asked to complete, or that the person in question actually did send you that email or text.
Too Good To be True? – If something sounds too good to be true, it probably is. While winning $1 million sounds incredible and you may be tempted to click on that link, take a moment to think about the situation. Most likely, this is a cybercriminal preying on your emotions.
The best defense against cybercriminals is using System 2 decision making – stopping and analyzing the situation before acting. Always ask yourself: is this too good to be true? Is this something that I have been asked to do in the past? Is this how the person or organization in question usually contacts me? If in doubt – reach out using a trusted method to the person or organization to confirm that what you have been told is legitimate.
Read the original article here
Check out their profile on CollabHub here
.png?width=600&height=187&name=Untitled%20design%20(2).png)